There’s a running joke regarding connected gadgets and the internet of things: “The ‘S’ in IoT stands for security.”
And yes, I’m aware there’s no “S” in IoT.
Oleg Šelajev, a lead developer for Oracle Labs, coined the phrase in 2016, and it pops up almost every time researchers find security flaws with a connected device. And it happens a lot. Think security cameras. Or toys. Or smart locks.
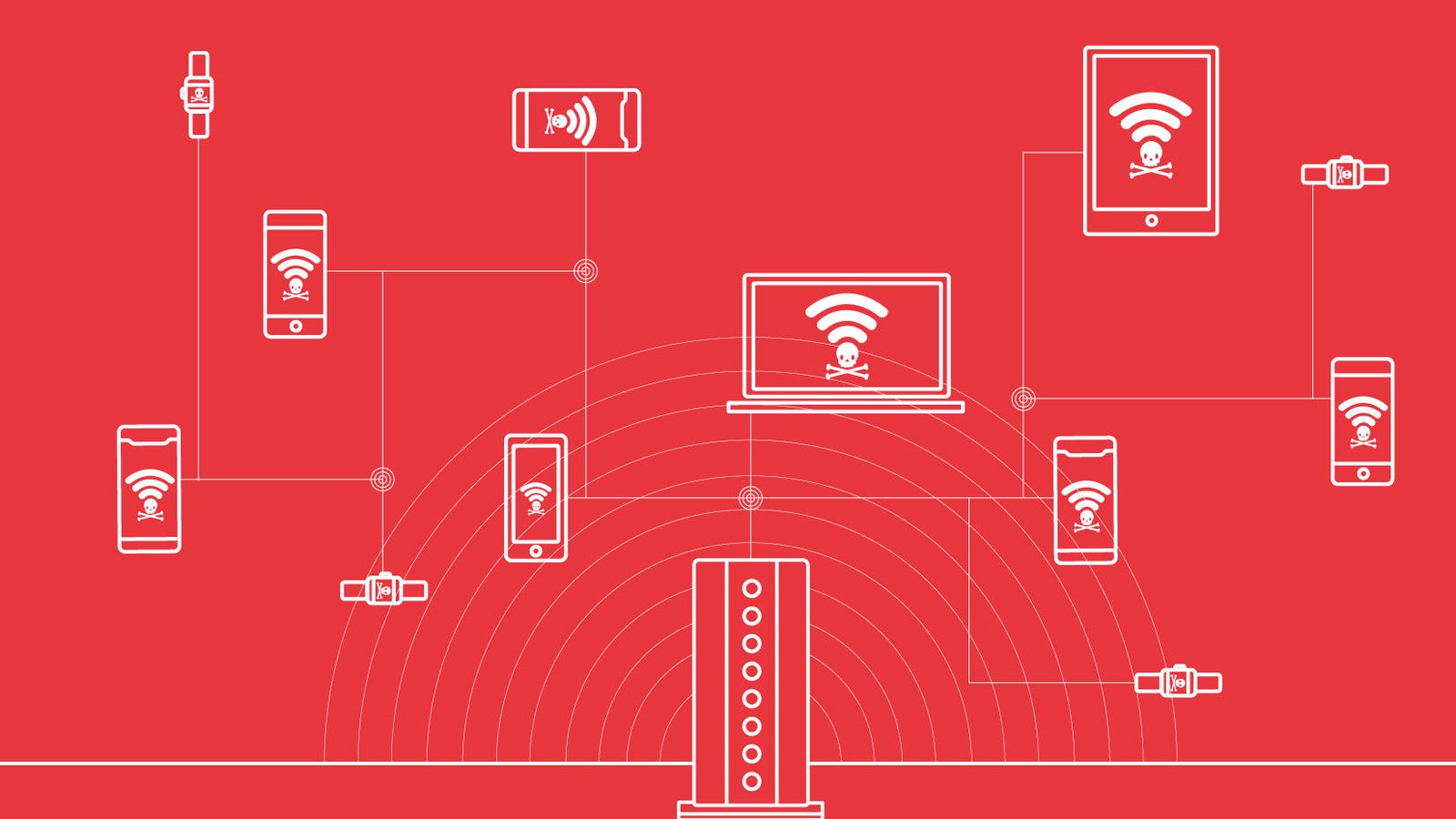
Yet homes, businesses and facilities are stocking up on more and more connected devices, the idea being to make people’s lives easier. The IoT sector is expected to grow to 20.4 billion devices by 2020, and businesses are expected to spend $134 billion annually by 2022 just on cybersecurity for IoT devices, according to Juniper Research.
But more connected devices means more potential vulnerabilities. And the security of these devices hasn’t gotten much better. Researchers have been warning about this issue for years, but the number of threats is only getting worse. The real problem is that no one’s listening.
“We demonstrated problems last year,” Denis Makrushin, a Kaspersky Lab researcher, said at his company’s Security Analyst Summit in Cancun, Mexico, earlier this month. “This year, it’s the same problems, but now with huge numbers.”
Even more distressing is the bigger threat to the more than 8.4 billion IoT devices already available today — especially as security vulnerabilities in old devices keep popping up. So even as politicians and the tech industry look to address this for new products, it’s the legacy gadgets that could prove most vulnerable. It was one of the key themes at the Kaspersky conference, where researchers exposed vulnerabilities affecting decades-old gas pumps, robots in malls and smart cameras for homes.
Panels at Kaspersky’s 10th annual summit in Mexico took place in windowless conference rooms just a stone’s throw away from Cancun’s sunny beaches. While couples were cooling off by the pool and families were playing in the sand at this popular vacation destination, security researchers were inside showing off vulnerabilities with the gadgets that increasingly run our lives.
It didn’t end with robots and gas stations. Other panels detailed how you could hack a yacht, a car, industrial control systems and hospital tech. The one common thread for all of this research: It wasn’t shiny, new gadgets with security flaws, but devices from years ago. These are the ones makers have moved on from, but people can still buy in stores.
Your typical hospital serves as a case study for how vulnerable we are. Kaspersky Lab’s researchers found 27,716 open entry points for a hacker. Yury Namestnikov, one such researcher, attributes this to a rise in internet-connected devices in hospitals, some of which might not even be medical equipment.
They found issues with the lighting systems, air-conditioning units and printers. Many of them were using out-of-date management software open to attacks. The researchers pointed out that the popular Cancun resort they were staying at might also have these same security issues.
“If you’re an administrator, you need to decide what kind of stuff needs to be on the internet,” Namestnikov said in an interview at the resort. “You need to make inventory, what’s connected and what you should protect.”
Hospitals were among the first victims hit by the WannaCry ransomware attack, preventing patients from getting urgent care while computer systems were locked up. Security is a major concern at hospitals, which hold sensitive data for attackers to target. But hospitals are increasingly embracing connected devices.
“They have to use new equipment to keep up, but they don’t understand a need to adopt security also,” Namestnikov said.
When companies aren’t building their devices with security in mind, it ends up falling on researchers to both find the mess and help clean it up.
There are always new places to find security vulnerabilities.
After successfully hacking the Pepper and Nao robots, Lucas Apa, a researcher from IOActive, said he was interested in a looking at Knightscope, the robot that notoriously was used to disperse the homeless in San Francisco and that comically was found drowned in a fountain in Washington, DC.
For Ido Naor, the Kaspersky researcher who discovered issues with more than 1,000 internet-connected gas stations, he’s always keeping an eye out.
“As researchers, we walk around the world, and check out everything,” Naor said. “Marks, logos, different types of devices we’ve never seen before, and it tickles our mind to look for information about it.”
The scariest thing: Plenty of hackers are probably just as curious.
Avots: CNET